Turn Assumptions into Trust
Do You Know What Your Partners Do With Your Data?
Assumed closes the downstream blind spot that brand integrity, compliance monitoring, and vendor‑oversight teams struggle with by using data seeding—artificial consumer contacts that move through your partner ecosystem just like real leads. This makes identifying compliance violations, brand risk, and affiliate data misuse dramatically more efficient and far more reliable.
TRY ASSUMED SEEDS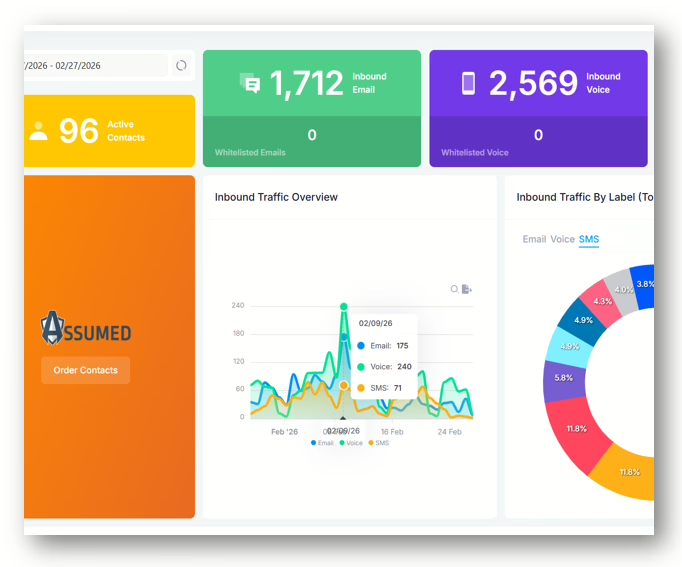
“What happens after the lead?”
Most teams still can’t answer this, and that’s the blind spot Assumed eliminates.

The Problem You Can’t See Is the One That Hurts You
Monitoring Isn’t Enough. Evidence Is What Protects Your Brand.
Your current tools show what partners intend to do. Assumed shows what they actually do after the click. Common things to uncover with data seeding are compliance failures, brand damage and regulatory exposures.
Real-time monitoring and unauthorized data use detection
Adherence to data handling best practices
Build trust and accountability among data partners
TRY ASSUMED FOR FREEWhere Your Current Monitoring Stops, Risk Begins
Your Monitoring Stack Covers the First Half, Assumed Covers the Second.
Reduce the risk of non-compliance penalties and build trust with clients by showing a commitment to data security.
Page scans catch misalignment, but not misconduct
QA checks disclosures, but not lead resale
Your clients deserve protection not assumptions
QUESTIONS? BOOK A CALL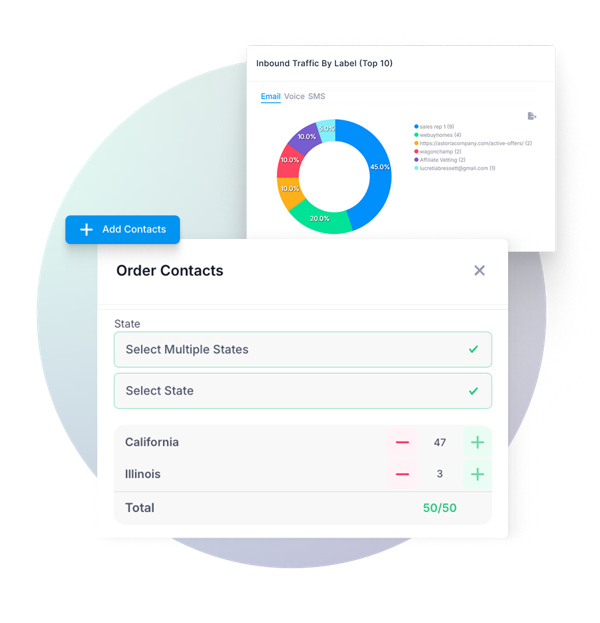
“Is anyone reselling or misusing our data?”
Without downstream visibility, you’re operating on assumptions, and assumptions create risk.

Who Assumed Helps
Built for Teams Responsible for Lead Generation, Brand Integrity and Compliance
Insert seeded data into datasets shared with third-party partners to track how your information is being used and detect any misuse or abuse. Watch that your partners handle your data responsibly and maintain trust in your business relationships.
Validate partner behavior with real evidence
Add downstream visibility your clients are already asking for
Ensure partners follow approved messaging and flows
Prove data stewardship and reduce regulatory exposure
TRY ASSUMEDYour Always‑On Downstream Evidence Generator
Assumed Seeds: The Missing Layer in Your Monitoring Stack
Seeds behave like real consumers — revealing what partners actually do with your leads.
Lead resale and unauthorized data sharing
Script deviations and misleading call flows
Unapproved remarketing emails
Off‑page behavior your tools can’t see
Hidden compliance failures that trigger FTC/CFPB/AG actions
GET STARTED
“You can’t fix what you can’t see.”
Assumed gives you the visibility to intervene early.
ONE SIMPLE SOLUTION. ENDLESS USE CASES.
Brand Integrity & Compliance Monitoring
Catch affiliate and partner misconduct with Assumed Seeds that page‑level tools can’t see.
Vendor Vetting & Ongoing Oversight
Validate that partners follow your rules, not just during onboarding, but continuously.
Affiliate & Partner Governance
Ensure partners follow approved messaging, disclosures and consumer flows.
Risk, Privacy & Regulatory Assurance
Demonstrate due diligence with evidence that withstands regulatory scrutiny.
How Seeds Work
It’s Easy to get started
1. Deploy Seeds
You create consumer profiles that flow through your partner ecosystem.
2. Reveal Behavior
Seeds receive calls, emails, texts, and outreach, all automatically recorded.
3. Review Evidence
Every interaction is timestamped, creating a chronological evidence trail that can be enriched with screenshots, labels and analyst notes.

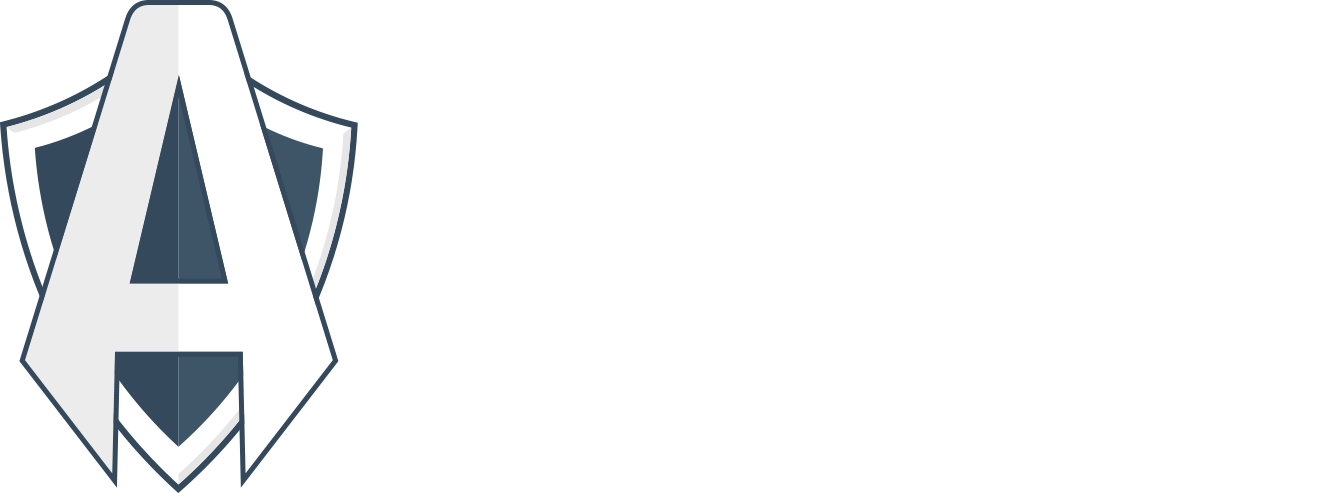
What You Get With Assumed
Timestamps
Precise timing for every message received, just like your inbox.
Labels & Classification
Apply labels to organize your work and tag contacts for investigation.
Evidence Trails
Build immutable, audit‑ready documentation.
Screenshots
Visual proof of the consumer experience by adding screenshots to your notes.
Analyst Notes
Add context and collaborate with your team.
Reports & Alerting
Know when something goes wrong downstream.
Don’t Take Our Word for it
Our Compliance-Minded Customers Had Already Figured it Out. Assumed Just Made it Better.
Our clients get it. They are monitoring affiliates, coaching partners, vetting vendors, auditing for compliance and much more with Assumed Seeds.
White Paper
Read our complete guide to vetting partners and discover how Assumed Seeds can help keep your affiliate and partner vetting processes on the right track.
Case Study
Explore how iRelo, a lead generation company in the auto transport and moving industries, has leveraged Assumed’s contact vetting solution to address the challenges of lead reselling, quality assurance and partner management.
More from Assumed
Check out our blog to find out how customers like Advanced Client Solutions are using Assumed to avoid the pitfalls of the lead gen industry, and subscribe to our newsletter for our latest perspectives on the issues that brought you here.
“Ready to ditch throw-away Gmail addresses, burner phones and spreadsheets?”
Take your affiliate vetting and monitoring processes to the next level with Assumed.