Turn Assumptions Into Trust With Assumed Seeds
Assumed is built for security-minded professionals, including CISOs, compliance officers, privacy staff, lawyers, auditors, marketing managers, call center customers, business owners and everyone who has a vested interest in protecting the sensitive data under their care.
Using Assumed Seeds is easy, just sign up, purchase contacts and start monitoring for data leaks, vetting your vendors or partners or any other ways Assumed Seeds can be used in minutes!
We provide artificial contacts – Assumed Seeds – as honey tokens for simple, effective data leak monitoring, vetting data partners, and validating consumer experiences. With Assumed, you can ensure that your partners handle their data as they claim, validate your lead/sales processes, and monitor your databases for unauthorized access or theft. Don’t just assume; verify with Assumed.
Improve your security posture with our
Data Seeding Solutions
Assumed’s intuitive data seeding solutions can be used whenever there is a need to vet new data partners or test a process and used continuously for data monitoring, auditing and compliance assurance.
What is Assumed Seeds?
Data seeding is a proactive security measure used to detect unauthorized data access, leaks, and breaches. Organizations can use data seeding techniques to track and monitor how data is being used, shared, and potentially misused.
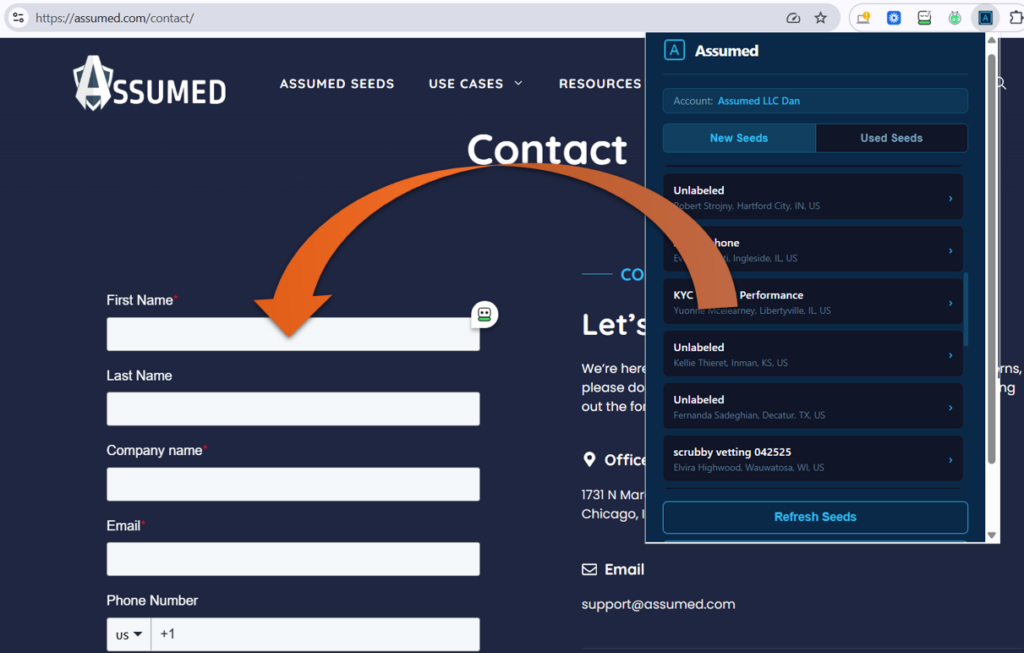
Assumed Seeds is a cost-effective and intuitive data seeding solution that utilizes artificial consumer contacts (seeds), or honey tokens, that can be used to monitor email and phone messages to detect indicators of data leaks, vet data partners, audit or validate contact processes, conduct research and much more.
Where can you use Assumed Seeds?
Assumed can be used whenever there is a need to vet new data partners or test a process and used continuously for data monitoring, auditing and compliance assurance.
Assumed Seeds can be planted just about anywhere sensitive data is stored or processed including CRMs, contact lists, lead generation platforms, marketing systems, honey pots or injected directly into online forms.
Why do you need a data seeding solution?
Whether you are trying to maintain compliance with various regulations such as TCPA or better align with security frameworks and best practices like the NIST CSF, Assumed can help you to identify and prevent data breaches, avoid abuse of customer data, minimize 3rd-party risk and provide assurance of the confidentiality and integrity of your data assets.
Are your partners treating your contacts with respect?
With Assumed, you can test how your vendors and partners handle the contacts they have. Our seeded contacts allow you to monitor emails, text messages and phone calls in real-time, alerting you to any excessive or irrelevant communication or unauthorized use of data under your care. These honey tokens allows you to ensure that your partners manage data as promised and adhere to best data handling practices.
Are your consumer marketing lists compromised?
With Assumed you will know! Detect unauthorized use of consumer data with our data leak monitoring solution. Data leak detection as simple as 1, 2, 3:
Purchase artificial contacts and
plant your seeds wherever your sensitive data is stored. You can place these leak-detecting contacts in your CRM, HR systems, mailing lists or anywhere else you store personal consumer or employee data.
If your top sales executive left the company and took your customer database with them, would you know?
With Assumed, you can monitor your databases for unauthorized access or theft. Our solution indicates a data breach or misuse of protected data, reveals insider threat activities, including theft of company-owned data, and validates sales, lead generation, and customer contact processes. If your decoy contact suddenly receives emails from your competitor, you know theft was involved.