Monitor Your Attack Surface. Detect Insider Threats. Test Your Defenses.
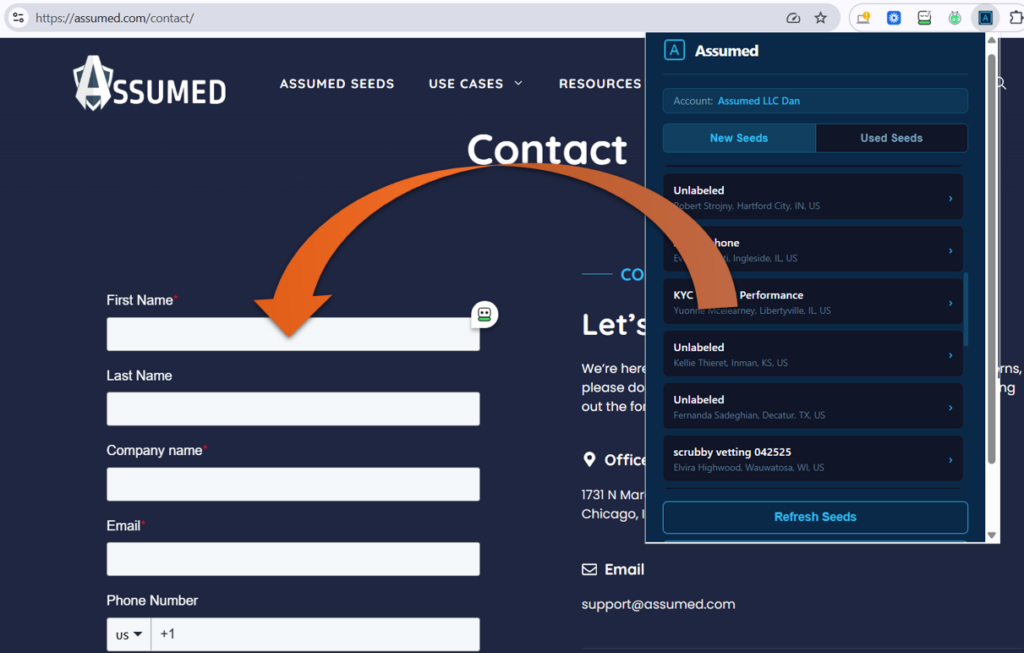
Use Assumed Seeds to proactively monitor your most vulnerable data assets and strengthen your security controls. Assumed Seeds are artificial contacts (honey tokens) that act as early warning systems, helping you detect data breaches, vet security partners and validate your defensive capabilities before attackers exploit them.
What’s at Stake in Your Security Operations?
Even your most sophisticated security stack has blind spots. Assumed helps you illuminate and eliminate these gaps.
Undetected Data Exfiltration
Is sensitive data leaving your organization without triggering alerts? Traditional monitoring misses subtle data theft and insider threats.
With Assumed Seeds planted in your databases and CRMs, you’ll know immediately when unauthorized access occurs. Our honey tokens provide forensic evidence of data breaches that conventional security tools miss.
Unvetted Security Partners
When MSSPs and security vendors claim they follow best practices, how do you verify? Assumed cuts through vendor promises with hard data.
Our Seeds document exactly how your security partners handle sensitive information, providing clear evidence of policy violations or data misuse that could compromise your entire security posture.
Compromised Contact Databases
Wondering if your customer data has already been breached? Assumed lets you monitor in real-time.
Whether seeding employee databases or customer contact lists, you’ll detect unauthorized access, data theft by departing employees, or shadow IT practices that bypass your security controls.
Get a Custom Assumed Walkthrough
We’ll show you how to integrate Assumed Seeds into your existing security operations to continuously monitor, test, and validate your defensive capabilities.
Monitor Like a SOC Analyst
Assumed gives you continuous visibility into your most critical data assets.
Real-time Breach Detection
Track every email, call, and text sent to your seeded contacts. Get instant alerts when honey tokens are accessed, indicating potential data breaches or insider threats.
Deploy in Minutes
Plant artificial contacts in databases, CRMs, and partner systems instantly. No complex integrations. No operational disruption. Immediate threat detection capabilities.
Granular Attribution
Label Seeds by system, partner, or campaign so you know exactly where breaches originate. Your incident response has never been this precise.

What Assumed Users Are Saying
Don’t take our word for it. Here’s what our customers have to say.
Moriah Smith – iRelo
“We already knew about the activity with clients, but Assumed has streamlined the process and made my
life easier!
The testing can happen a lot more frequently, and we can better manage the data to pinpoint stress
points with clients and consumers. I plan only to use Assumed for the testing of clients and our due diligence
process.
The benefits of having all testing in one place and a place to go to retrieve the data have been instrumental for our data collection, review and the management of our clients. I recommend Assumed to other lead generation companies as it helps with organization and ensures that your leads and data are used properly and fairly for all on the campaign.”
George Hurley – Advance Client Solutions
“If you’re in the lead gen space and want to sleep easier at night, you should be using Assumed.
Even if it’s just to settle your own mind, knowing your partners are doing what they should be doing is invaluable.”
Win Big Against Advanced Threats
Assumed helps you stay ahead of attackers by providing direct evidence of compromise attempts and security control failures. Use deception technology to enhance your monitoring capabilities and show your organization how comprehensive cyber defense is done.